Last modified:
Note
-
The basic IP allowlist feature is available from firmware 25.1.8 and higher.
-
For comprehensive firewall capabilities, firmware version 28.0.2 of higher is required.
-
Starting from this firmware version, the menu item IP allowlist is replaced by Firewall.
-
Existing IP allowlist configurations are automatically updated when you upgrade the firmware.
Cybersecurity is critical in the renewable energy sector. Implementing a firewall helps protect your system by defining allowed and forbidden network traffic. In the firewall configuration, you can create rules to allow or block traffic between devices and the virtual networks organized under Settings > VLAN. The firewall only affects network traffic via the blue'Log’s Ethernet interface.
VCOM USERS If you use VCOM as a backup, note that firewall configurations are not automatically included in VCOM backups. To prevent data loss, we strongly recommend:
-
Enabling VCOM backup
-
Performing a manual backup before enabling the firewall.
This ensures that all configurations can be restored in case of any incorrect firewall configuration. See also Backup and restore
Set up firewall rules
Prerequisites
-
You are using blue'Log XC or blue'Log XM
-
Firmware 28.0.2 or higher is installed
-
You have completed the necessary actions described under VLAN.
-
VCOM USERS You have performed a VCOM backup. See Backup and restore.
Steps
-
Go to Settings > Firewall and select the Plus icon to add a rule.
-
Select the protocol: Depending on your firmware version, the following will be available: TCP, UDP, ICMP (firmware 29.1.10 or higher).
-
Select the interface from the available network interfaces, including configured VLANs.
-
Select the direction: incoming or outgoing.
-
Enter the source IP address. CIDR notation, e.g. “/16", is supported.
-
Enter the source port. Hover over the Info icon next to Source port for options.
-
In the Action column, select whether to allow or forbid the action. If forbidden, all network traffic via the blue'Log Ethernet interface will be blocked.
-
Optional: Add comment for the rule. This helps all users to review and manage the firewall rules, e.g. if you need to re-configure the firewall.
-
Select the Disk icon to save the rule.
-
Firewall rule settings are stored until the firewall is activated. When you have entered and reviewed your rules, activate the Firewall toggle to activate the firewall.
Note
To prevent accidental lockout from the web interface, the following ports cannot be configured:
-
Port 80 (in/out)
-
Port 22 (in/out)
-
Port 443 (in/out)
Further actions
Set order of firewall rules
You can change the order in which the firewall rules are applied by selecting the up/down arrows in the Priority column in the table.
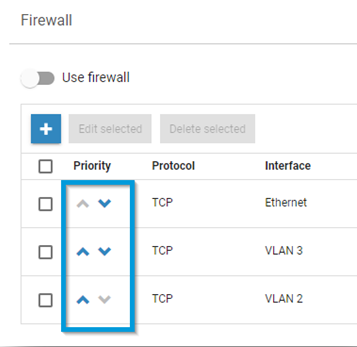
Edit or delete firewall rules
-
To edit or delete a firewall rule, use the options next to its name in the list.
-
For bulk actions, select multiple rules by ticking the checkboxes next to them. Select Edit selected or Delete selected.